OUR TECH BLOG
Stay Current With What’s New in IT
Consider Future Link Your IT Resource During This Challenging Time
When many states implemented shelter-in-place...
Email is the Main Entry Point for Cyber Attacks. Are You Secure?
In 2019, more than half of all IT security...
Think You Have Nothing to Hide? Think Again—and Protect Yourself From Ransomware
Even if you consider yourself an open book, with...
Insider Security Threats: Preventing (and Remediating) Employees’ Inadvertent Data Leaks
Many IT professionals rightly focus on external...
Don’t Miss This Once-in-a-Lifetime Investment Opportunity!
Dearest Lovely Friend, My name is Mr. Nweni...
Team Member Spotlight: Nick Maycock
Nick Maycock admits that climbing water towers...
Why Backups are the Foundation of Your Cybersecurity Plan
March 31, 2020 marks the first World Backup Day...
What to Know About Switching to a Local ISP
Although you don't have to switch your internet...
“Compliant” Doesn’t Equal “Secure” in the Internet Age
The ease with which information can be instantly...
Team Member Spotlight: Jimi, Internet Sales & Service
Like many of the professionals at Future Link,...
Protecting Your Email and the Data in It
Each day, nearly 300 billion emails are sent and...
Cybersecurity Threats Your Municipality Can’t Ignore
As your municipality budgets for the next fiscal...
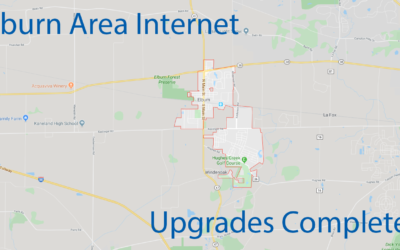
Elburn Area Internet Upgrades Completed
Announcement... Future Link Internet has...
The Real Goal of Hackers: Breaking Things Down
When you wake up in the morning and read about...
How Quickly Are You Updating Your Firewall?
Do you know why your mobile carrier constantly...
Three Top Resolutions to Protect Your Data in 2020
In light of the statistic that up to 80 percent...
Want warm fuzzies all year round? Work with a team that’s here to stay
The holiday season and first flurries of snow...
Team member spotlight: Tod Sercich, Technician
Got Plugins? How fraudsters use these hidden doors to hack your website.
By allowing nearly endless levels of...
Security Threats Go Both Ways: Why web security isn’t just an “inbound” problem.
Many of the most well-known web security...